Behavioural Targeting wird oft aus der Sicht eines Marketingexperten behandelt. Dieser Artikel ist der Versuch etwas Licht in die Techniken zu bringen. Vielen Dank an Michael Kassner.
Behavioral targeting, to say the least, is an interesting concept. It may change how all of us view and use the Internet. Knowing that, Id hope everyone would want to understand what its all about. Briefly, behavioral targeting first determines what you like, based on where you go on the Internet. Then, behavioral targeting selects advertisements that are most likely to influence you, displaying them on the new web pages you ask for.
Before we get too much deeper into behavioral targeting, I need to point out some related technology that makes behavioral targeting possible. Behavioral targeting only became feasible when Deep Packet Inspection (DPI) matured into an established technology. Therefore, its important to comprehend what DPI is. To help in that regard, please refer to a recent article of mine called Deep Packet Inspection: What You Need to Know. I know it seems like a shameless plug, but it helps if were all on the same page.
The infamous cookie
The next piece of the puzzle we need to understand is the much-maligned cookie. Cookies are benign text files that are sent to the web browser from the web server thats hosting the web pages being queried. Cookies have multiple purposes: they allow automatic authentication, keep track of the browsers session state, and identify the user/web browser combination to the web server. The fact that cookies can identify the user/web browser combination is paramount to our discussion about behavioral targeting, because the behavioral targeting process installs additional cookies specifically to track what web pages have been viewed. Thats why cookies are so important and why Id like to describe how a cookie is installed:
- The process starts when I type the URL of a web site into the web browser.
- The browser will check the computers hard drive for a cookie associated with the web site I just entered. If it finds the appropriate cookie, the browser will send the cookie information along with the URL to the web server controlling the web site being queried. If the browser doesnt find a cookie, no data is sent.
- The web server receives the request for a page. It then checks to see if a cookie was sent as well. If so, the web server can use that information to tailor the web page specifically for me.
- If the web server didnt receive a cookie, it knows that I havent visited the site before. The web server then creates a new ID for me in the web servers database and sends a cookie in the header for the web page to the computer Im using. My computer then stores the cookie on the hard drive. From that point on Im uniquely identified when I ask for web pages from that particular web server.
We now have all the relevant pieces, so lets get to the important stuff. Behavioral targeting is an application that uses information it has gleaned from our web-browsing habits to display ads it thinks wed like to see. The process starts with companies like Phorm or NebuAd (behavioral targeting development companies) talking to our ISPs, offering the ISPs money if they will allow Phorm or NebuAd to install equipment in the main traffic stream of the ISP. This equipment serves two purposes:
- It inserts a Phorm or NebuAd cookie that uniquely identifies each ISP subscriber and is associated with every cookie domain that has been issued to the subscriber.
- By using DPI equipment, reads every web page that the subscriber has asked for and creates a profile of the subscribers interests based on a predetermined checklist.
Phorms approach
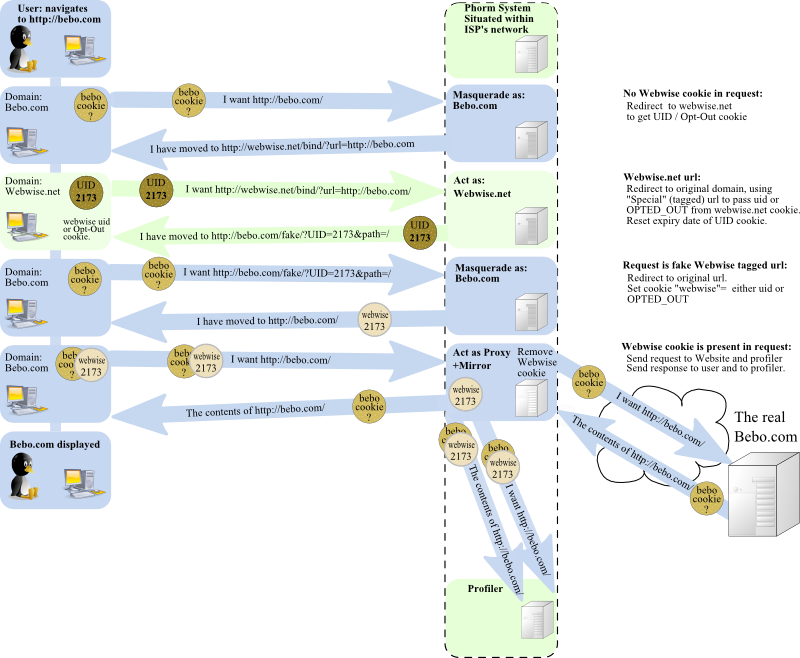
The subscriber profile is of obvious interest to advertising firms why serve ads about baby diapers to someone interested in joining AARP? The advertising firms negotiate with Phorm or NebuAd to provide content through the behavioral targeting application. Thereafter, no matter where the subscriber goes on the Internet, those specific ads will show up on the web page being served to the subscriber. To help clarify this, lets take a look at the process (diagram courtesy of Wikipedia) Phorm uses to set up behavioral targeting:
- I want to go to www.techrepublic.com, so I type the appropriate URL in my browser and the browser sends the query out to the Internet.
- My ISP receives the request, normally passing the query on. Since theres Phorm equipment in the data stream, it intercepts my query for www.techrepublic.com.
- The Phorm application then checks to see if theres a Webwise.net cookie (a domain name owned by Phorm) associated with the Techrepublic.com domain.
- Theres not one initially since the Phorm equipment has just been installed. Therefore, Phorm blocks access to www.techrepublic.com.
- Now a Phorm server at the ISP steps in and pretends to be a web server at www.techrepublic.com, returning a 307-Temporary Redirect to my web browser. The 307 redirect tells my browser that the URL I asked for has been relocated temporarily to a different location.
- My browser now thinks that www.techrepublic.com has moved to www.webwise.net, so it makes a redirection query to www.webwise.net. If my web browser locates a Webwise domain cookie it will also be attached to the redirection query. Phorm then knows who I am by the unique ID associated with the Webwise.net domain cookie.
- If there isnt a Webwise domain cookie, the Phorm server will assign one to me and send it back to my browser in another 307 temporary redirect response to a fake www.techrepublic.com page that is on the Phorm server. Therefore, if I didnt have a Webwise.net cookie, I do now and its a first-party cookie.
- Next, my web browser sends a redirection query to the fake www.techrepublic.com page. The Phorm server once again steps in and pretends to be the web server at www.techrepublic.com. Remember the browser thinks its sending a query to www.techrepublic.com and theres still the unique Webwise user ID in the query. The Phorm server now sends the final 307 temporary redirect response to my web browser telling it to go to the actual www.techrepublic.com web page. This part is important: The Phorm server also sends back a Webwise cookie, but its placed in the Techrepublic.com domain and becomes another first-party cookie.
- Finally, my web browser sends a query to www.techrepublic.com and it appears that it will make it this time. The query has a unique payload of cookies as well, one for the Techrepublic.com domain and one for the Webwise.net domain.
- The Phorm equipment at my ISP intercepts this query and the Webwise.net domain cookie is stripped off before the query actually proceeds to the Techrepublic.com web server. This appears to take place to avoid public visibility of the Webwise.net cookie, as it shouldnt be on a www.techrepublic.com query.
- The contents from my query to www.techrepublic.com come back and are intercepted by Phorm equipment. A copy of the information along with my Techrepublic.com domain and Webwise.net domain cookies are sent to a secondary piece of Phorm equipment.
- The secondary Phorm equipment scans my Techrepublic.com web page for key information that will be added to their browsing profile about me.
Sorry for the long, drawn-out description, but thats exactly what takes place every time a web browser sends out a query. In this way, Phorm knows exactly where I go on the Internet and what Im looking at. With these profiles, Phorm, for a fee, will tell advertising firms what ads to place on the web pages being served to me. The company states this whole process is anonymous, but that requires trust in what Phorm says, as the Phorm application is proprietary and not available for peer review. I dont have an opinion one way or the other as to the claims of anonymity by Phorm. As mentioned earlier, Im just concerned that most users are not aware of this technology, and I want to correct that.
NebuAds approach
NebuAd is another major player in behavioral targeting. Their process is slightly different, and Id like to explain the differences, even though the results are the same. The NebuAd equipment is also placed in the ISPs main data stream, but NebuAd doesnt use the cookie shuffle like Phorm. NebuAd, to their credit, uses a very innovative approach Ill explain by using the following example:
- I want to go to www.techrepublic.com, so I type the appropriate URL in my browser and the browser sends the query out to the Internet.
- My ISP receives the request and passes the query on to www.techrepublic.com (different from Phorm).
- The web server at www.techrepublic.com replies to my web browsers query with the appropriate web page.
- The NebuAd equipment at my ISP is monitoring this exchange and as the last packet reaches the ISP, the NebuAd application injects one packet to the end of the traffic from the web server at www.techrepublic.com.
- This final packet contains JavaScript. The script causes my web browser to go and retrieve scripting code at a NebuAd web site.
- My web browser then runs the script and a NebuAd cookie is planted on my computer.
The NebuAd cookie is similar to the Phorm cookie in that it uniquely identifies me and allows the NebuAd applications located at my ISP to track my Internet activity, scan the returned web pages, and create a profile thats of interest to advertisers. At this point, Phorm and NebuAd are almost identical.
Whats it all mean
Thats the ultimate question, and Ill leave that to the pundits who are much more knowledgeable than I am. As I mentioned, my goal was to make you aware of whats coming. Im not sure I want a business entity tracking my every move on the Internet. My government, sure thats a different story. They arent doing it for monetary gain; they are protecting me. That being said, I do understand the need for advertising. Part of my professional existence depends on advertisements. Im just not sure being this invasive is the answer.
Also, I suspect that this business model will place the advertising world in some sort of turmoil. For instance, who gets to decide what ads are displayed when I go to Techrepublic.com? TechRepublic or someone paying my ISP? For more insight into how this topic is playing out, I suggest that you listen to Steve Gibson of GRC.com and Leo LaPorte from Twit.TV (Anmerkung 31.01.2016: Link entfernt, da nicht mehr verfügbar). They cohost a series called Security Now and have put together several of their pod casts that explain relevant pieces of behavioral targeting. Id especially recommend listening to the podcast, Episode 153: DePhormed Politics, where Steve and Leo have an enlightening discussion with Alexander Hanff, a technologist and anti-Phorm activist from the UK.
Preventative measures
There are options that you can use to avoid behavioral targeting cookies and DPI scrutiny. Encrypted tunnels through your ISP disallow the installation of behavioral targeting cookies. Also using VPNs, whether they are IPsec, L2TP, or SSL, will negate any effort by DPI to decipher the encrypted traffic. E-mail is another subject, and once again the only for sure way to ensure its privacy is to encrypt the message. There are not a whole lot of options, but thats because behavioral targeting applications are being placed only one hop away from your network perimeter.
Final thoughts
Whew, this is a tough subject. I know that opinions about behavioral targeting will run from A to Z, and thats good. Im not even sure what my final thoughts are. What bothered me was the lack of information about behavioral targeting. Hopefully, I was able to change that with this article.